CAVEON SECURITY INSIGHTS BLOG
The World's Only Test Security Blog
Pull up a chair among Caveon's experts in psychometrics, psychology, data science, test security, law, education, and oh-so-many other fields and join in the conversation about all things test security.
What Are Proxy Test Takers (And How to Stop Them)
Posted by David Foster, Ph.D.
updated over a week ago
Introduction
Proxy test takers can be persuasive. Just last week, when scrolling through social media, I came across this post (blurred for privacy purposes):
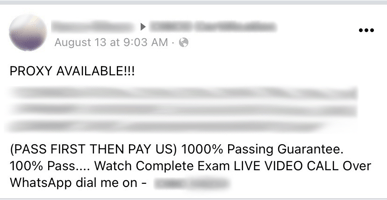
The listing notes more than a dozen exams for which the group offers proxy testing services, with a guaranteed passing score.
Solicitations like these are painfully common. Scroll through social media groups for specific certifications, and you’ll likely find several recent posts offering proxy test-taking services. Type “proxy test takers” into a search engine, and you’ll find hundreds of websites that guarantee passing scores through proxy services. Spend a little time on LinkedIn, and you’ll likely get sent personalized offers to have someone take an exam in your place (perhaps even the exam you developed! Check out these thoughtful responses for when that happens).
What is Proxy Testing?
Proxy test taking is when an examinee cheats by having someone more knowledgeable than they (whether a colleague, a friend, or a paid professional service) take their exam in for them. Proxy testing is one of six major types of cheating threats (all of those threats are outlined in this white paper) that pose a risk to your testing program. It is a particularly egregious form of cheating, and it is both incredibly effective and surprisingly common. The proxy tester can be either an amateur (a friend who is taking the exam as a favor) or a professional (an individual who is paid to sit the test). Luckily, there are effective ways to stop proxy testing, and even catch those who have already used it to cheat on your exam.
The Characteristics of Proxy Testing
1. It Can Be Done by Either Amateurs or Professionals
It is true that “in practice, [proxy test taking] often means an individual [is] sending a colleague or subordinate employee to complete the test on their behalf” (Kleeman, 2019). But the reality of who acts as a proxy is far more complicated and more serious.
Using a proxy test taker can certainly be as informal as asking a classmate or colleague to take an exam in your place. In this case, these are “amateur” proxies, likely helping out a friend or acquaintance. These amateur proxies typically are not doing it for financial gain. (Even if they are compensated for their effort, being a proxy likely isn’t their full-time job or even a regular side gig).
In contrast, professional proxies (also referred to as “hired guns”) are companies or individuals that offer proxy testing as a professional service. They advertise and promote their services (through their website, advertisements on social media pages, direct messages on LinkedIn, etc.). Some specialize in a few exams, while others offer a wide range of exams they are willing to proxy. For a small fee (or sometimes a not-so-small fee with some proxy companies charging in the thousands or tens of thousands of dollars), you are guaranteed a passing score by a proxy examinee who is an expert in the exam content.
Consider an example given by a Caveon security expert in this article by Robert L. Mitchell:
A few years ago, a large IT certification provider engaged Caveon to hire a proxy and attempt to pass the test without being caught. “The certification program paid us, we paid a proxy service, and one of my colleagues earned a prestigious certification—even though he had no background,” says Steve Addicott. The price to cheat: A $1,000 check wired through Western Union. The terms were 50% down, with the balance paid after the job was completed.
As you can see, it can be easy to successfully employ a proxy test taker and pass a high-stakes exam.
2. It Is an Effective Way to Cheat
Regardless of whether someone uses an amateur or a professional proxy, it is important to understand that using proxies is an incredibly effective method of cheating. Effective in this instance means that, so long as the proxy isn’t caught, the cheater is essentially guaranteed a passing score.
Compare proxy services to examinee pre-knowledge gained from purchasing an answer key online. Both methods of cheating require purchasing help on the test. However, on the day of testing, an individual using pre-knowledge cannot control whether the questions they memorized will actually be seen on the exam. If there are multiple forms or a large item bank, the pre-knowledge might only be minimally effective. The cheater might not see many questions that they memorized. As a result, they cannot be assured of getting a great score. In comparison, proxy testing is effective whether or not the content of the exam changes. The proxy is an expert in the exam content—so no matter how large the item bank, how many forms, or how often questions are republished, the proxy test taker will still get a passing score.
Because of its nearly fail-proof design, proxy testing is so dangerous and so tempting to individuals looking to cheat. Most methods we use to prevent cheating—such as secure exam design (like those described in our ultimate guide), rapid republishing, etc.—are ineffective against proxies. The individual sitting down to take the test really does know the content of the exam; they just aren’t the examinee they are pretending to be.
3. It Is Common
While proxy testing can sound like the plot of a movie (and it has been), it is unfortunately more prevalent in real life than we often want to acknowledge or admit. Just look at the number of proxy testing services that can be found using a simple google search. The number of companies actively advertising their services on the internet is staggering. Just imagine how many others are operating under the radar, only to be found by word of mouth, in closed forums, or through private messages. The total number is likely overwhelming.
Next, consider the public scandals that have emerged in recent years. From 20 high school students paying others to take the SAT and ACT to the Operation Variety Blues Scandal, where an individual was paid $10,000 each to take the SAT for 36 students. There are even entire Reddit threads dedicated to individuals sharing stories of others to taking high-stakes college exams for them. But instances of proxy testing don't stay out of the news for long (jump ahead to this section to learn why).
Numerous investigations have shown the sheer extent of proxy testing. In 2020, PR Group Topline Comms conducted an investigation. They discovered that, since 2000, a single proxy testing company had sent more than 5,000 proxies to sit for certification examinations for many high-stakes exams. In 2008, officials at Cisco and Pearson VUE announced that after an 8-month-long investigation that monitored hundreds of thousands of exams, they discovered that “one in 200 exams was taken by a proxy, not the actual candidate.”
This is just the tip of the iceberg. Even given the number of companies offering proxy services, the scandals that dominate news headlines, and the investigations done on proxy testing—the sheer number of proxy-produced exam scores that we don’t know about is likely far higher than testing organizations even suspect.
How Can You Stop Proxy Testing?
The good news is that there are proactive steps you can take to stop proxy testing in its tracks. Let’s divide these recommendations into the three categories of the test security process—security measures that prevent proxy testing, deter proxy testing, and detect + react to proxy testing on your exams.
1. Preventing Proxy Testing: Rigorous Authentication Procedures
If you want to prevent proxy testing (that is, actually stop proxy test takers from being able to sit an exam for somebody else, rather than just catching them after the fact), you need to employ rigorous candidate authentication procedures. Proxies can only succeed if they can trick your team into thinking that they are the real candidate. They do this mainly by bypassing your identification and authentication measures.
First Identify Candidates
How can you authenticate your test takers? The first step is to think beyond simply identifying your candidates. Identification is simply the process of someone claiming to be a specific person. An examinee often identifies themselves by having an email address with the test taker’s name or by presenting school- or government-issued ID card. However, both methods are easily manipulated. For example, simply comparing an examinee’s face to an ID is not enough—it’s not enough over a webcam (if testing remotely), and it’s not enough in person. This is because it is simply too easy to photoshop the candidate’s name onto a fake ID and pair it with the proxy’s photograph. (There are even services on the internet that provide counterfeit IDs that are almost undetectable by the human eye, making it nearly impossible for even well-trained eyes—including those from law enforcement—to discern.) Add a webcam with poor visual quality for remote tests, and you’ve got an easy-to-bypass method for getting your proxy test taker into the exam.
Then Authenticate Candidates
Instead, you should focus your efforts on authenticating the examinee. Authentication is a verification step, not an identification step. Authentication doesn’t just ask, “Who are you,” It takes the additional step and asks, “Are you really who you say you are?” Therefore, when administering exams, you should first identify who the candidate says they are, and then authenticate that the person showing up for the test is indeed who they say they are; that they are actually the authorized individual you’re expecting to take the exam.
Use Biometrics
How can you identify and authenticate examinees? Having a rigorous authentication process in place is the first step in preventing proxy testers from bypassing your security and successfully taking an exam for somebody else. There are many types of biometrics—including fingerprints and keystroke analyses—that will effectively help you authenticate individuals. If you do opt for a biometric authentication system, ensure that it operates using a 1:1 method. That is:
-
-
- Require candidates to provide biometrics when registering for the exam, training course, or university
- Require biometrics when the candidate begins an examination
- Compare the two sets of biometrics to ensure the candidate is who they say they are.
-
Keep in mind that the authentication process can have very real implications for candidate privacy. Therefore, always make sure your biometric system aligns with strict privacy policies.
2. Deterring Proxy Testing: Effective Communication Practices
An often overlooked, but surprisingly effective, method for securing your exams and stopping proxy test taking is deterrence. Think of deterrence as a communication plan meant to discourage and inhibit test takers from cheating. Deterrence can be as simple as letting would-be test cheats and thieves know that they will get caught and that there are consequences to their actions.
In the case of proxy testing, deterrent communications are designed to convince 1) the individual hiring the proxy and 2) the proxy themselves that the odds of getting caught are higher than they should be willing to risk, and that the consequences for getting caught are untenable. Essentially, you convince them that it is too risky even to try. Specifically, we recommend that you:
-
- Tell examinees how you detect and prevent cheating
- Show examinees that the likelihood of getting caught is high
- Establish doubt in the minds of would-be wrongdoers whether they’d even benefit from attempting to cheat—let alone get away with it afterward.
There are many, many deterrent tactics you can use to accomplish this. From signing honor codes (minimally effective), to publishing the effectiveness and range of all your security measures (more effective), to punishing cheaters and actively broadcasting the consequences that were netted out (even more effective). The options are many. It is only a matter of finding the ones that are best for your program. (You can view this article for a list of deterrent examples, or you can learn more about deterrence in these curated articles.)
3. Detecting + Reacting to Proxy Testing: Data Forensics & Web Monitoring
Even with the most rigorous authentication methods and aggressive deterrence methods, it is likely that some proxy testing will get past your defenses. (Such is the nature of all security.) This is where detection + reaction methods come into play. The Detection + Reaction Process is one streamlined, cohesive measure designed to 1) catch cheating and theft that managed to get through your initial line of security, and then 2) respond appropriately and efficiently to the incident. You can learn more about the detection + reaction process as one streamlined step in this article.
Utilize Data Forensics
How can you detect and properly react to proxy testing? First off, make sure your program is utilizing data forensics. Data forensics is a fraud detection method that regularly analyzes your testing data and effectively uncovers cheating and test fraud. These forensic analyses are specifically effective at revealing the illicit activity of proxy test takers. Their data let you know (with confidence) which honest examinees earned their scores, and which scores were achieved by proxy test takers. The forensic results then allow you to apply the appropriate sanctions against both the examinee and the proxy—ranging from invalidating scores to seeking legal recourse. When utilizing data forensics, always remember to publicize its consequences in order to boost your deterrence measures, as listed above!)
Monitor the Web
Web monitoring is another effective method that enables you to detect and react to cheating. There are professional services (like this one) that constantly scour the internet, social media platforms, and messaging apps to uncover cheating and test theft. Web monitoring can even uncover the companies and/or individuals offering proxy services for your exam. It can also enable you to understand how likely the threat of proxy testing is to your program (are lots of companies offering to proxy your test, or just a few?). Once you’ve identified testing malfeasance through web scraping, you can then use it to help shut down the proxy organizations. Then, through data forensics, you can locate exactly which examinees have utilized proxy testing and react appropriately.
Conclusion
This article serves as a deep dive into the threat of proxy testing. It discusses what proxy test taking is and how to stop it.
Proxy test takers participate in an egregious form of cheating. Unfortunately, proxy testing is both effective and surprisingly common. When fighting proxy test takers, don’t be overwhelmed by the process; know there are viable solutions for keeping your tests scores safe. Take a moment to consider the options laid out above, and then enjoy this tongue-in-cheek infographic on how to respond if you (like us) are ever approached by a proxy test taker. As we’ve learned, saying “I could have sworn I saw your name on a test fraud most-wanted list” is just the right start to stopping proxy testing.
David Foster, Ph.D.
A psychologist and psychometrician, David has spent 37 years in the measurement industry. During the past decade, amid rising concerns about fairness in testing, David has focused on changing the design of items and tests to eliminate the debilitating consequences of cheating and testwiseness. He graduated from Brigham Young University in 1977 with a Ph.D. in Experimental Psychology, and completed a Biopsychology post-doctoral fellowship at Florida State University. In 2003, David co-founded the industry’s first test security company, Caveon. Under David’s guidance, Caveon has created new security tools, analyses, and services to protect its clients’ exams. He has served on numerous boards and committees, including ATP, ANSI, and ITC. David also founded the Performance Testing Council in order to raise awareness of the principles required for quality skill measurement. He has authored numerous articles for industry publications and journals, and has presented extensively at industry conferences.
View all articlesAbout Caveon
For more than 18 years, Caveon Test Security has driven the discussion and practice of exam security in the testing industry. Today, as the recognized leader in the field, we have expanded our offerings to encompass innovative solutions and technologies that provide comprehensive protection: Solutions designed to detect, deter, and even prevent test fraud.
Posts by Topic
- Test Security Basics (34)
- Detection Measures (29)
- K-12 Education (27)
- Online Exams (21)
- Test Security Plan (21)
- Higher Education (20)
- Prevention Measures (20)
- Test Security Consulting (20)
- Certification (19)
- Exam Development (19)
- Deterrence Measures (15)
- Medical Licensure (15)
- Web Monitoring (12)
- DOMC™ (11)
- Data Forensics (11)
- Investigating Security Incidents (11)
- Test Security Stories (9)
- Security Incident Response Plan (8)
- Monitoring Test Administration (7)
- SmartItem™ (7)
- Automated Item Generation (AIG) (6)
- Braindumps (6)
- Proctoring (4)
- DMCA Letters (2)
Recent Posts
SUBSCRIBE TO OUR NEWSLETTER
Get expert knowledge delivered straight to your inbox, including exclusive access to industry publications and Caveon's subscriber-only resource, The Lockbox.


